Should Password Policies Prioritise Length or Complexity?
Table of Contents

Open any penetration test report and weak passwords consistently appear amongst the most common findings. But here’s the funky part: many of these “weak” passwords can technically meet complexity requirements. They have uppercase letters, lowercase letters, numbers, and special characters. Yet pentesters crack them in minutes.
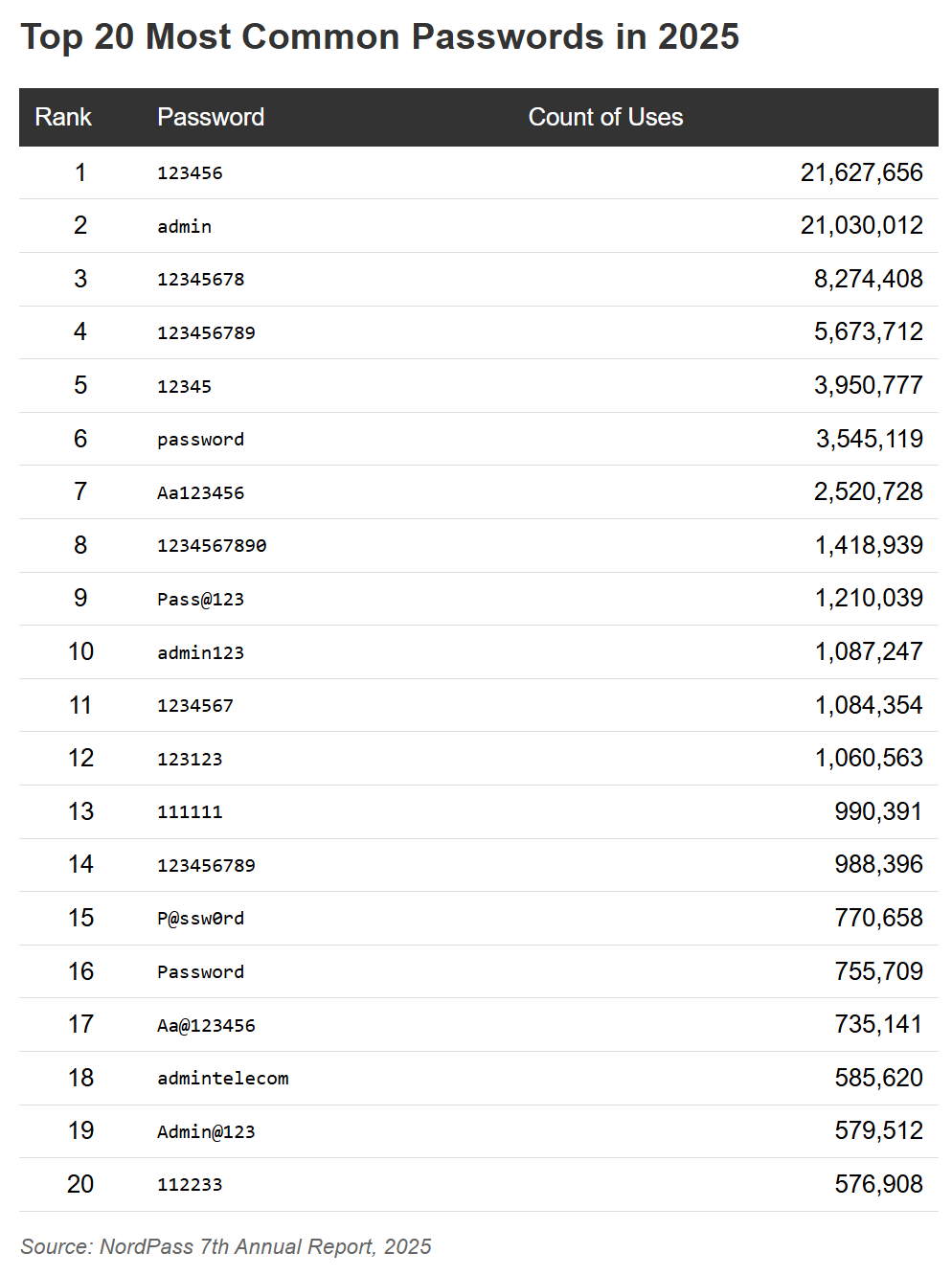
The problem isn’t that organisations lack password policies. It’s that most policies focus on the wrong thing. For years, security guidance has emphasised complexity: mix uppercase and lowercase, add numbers, throw in special characters. The result? Passwords like “Welcome2026!” that feel secure but crack quickly. Meanwhile, “correct-horse-battery-staple” would take centuries to crack using the same tools. According to NordPass’s 2025 analysis of the most common passwords, millions continue to use easily crackable credentials.
The difference comes down to password entropy.
Okay, But What Is Password Entropy Anyway??
Entropy measures unpredictability. It’s not about how complex a password looks to humans, it’s about how many possible combinations an attacker must try. Higher entropy means more possible combinations and more time required to crack the password.
Entropy increases dramatically with length, but only marginally with complexity within a fixed length.
A typical “complex” 8-character password might have 218 trillion possible combinations. Modern cracking rigs can test billions of combinations per second, breaking 8-character passwords in hours to days with consumer-grade hardware.
A 20-character password using only lowercase letters has over 19 quadrillion possible combinations. Even with a smaller character set (26 letters instead of 95 possible characters), the additional length creates exponentially more possibilities.
Traditional Complexity Rules Are Kinda Hit-Or-Miss
Traditional complexity rules emerged from good intentions but flawed assumptions. The thinking: if passwords must include multiple character types, they become harder to guess. In practice, humans respond predictably.
Forced to include an uppercase letter? Most capitalise the first letter. Required to add a number? It goes at the end as “1”, “123”, or the current year. Need a special character? Expect “!” or “@” in predictable positions. Cracking tools specifically target these patterns.
The result is passwords that appear complex but have low entropy because they follow predictable patterns. “Password1!” technically meets most complexity requirements. It’s also one of the first passwords any cracking tool will try.
Meanwhile, “purple-elephant-dancing-microscope” violates most complexity rules yet has higher entropy and is genuinely harder to crack. The complexity rules optimise for the wrong metric.
What Organisations Can Do
If password issues keep appearing in reports, the answer is layering multiple defences together.

Together, lengthy passwords, password managers, and MFA create defence-in-depth that significantly raises the bar for attackers.
Need help assessing your organisation’s password security? Our penetration testing services identify weak passwords and authentication gaps before attackers do. Contact us to discuss how we can help strengthen your security posture.